A couple weeks ago GoDaddy experienced yet another security hack that tricked GoDaddy employees into handing ownership and control of multiple web domains over to hackers. Inadvertently assisting in attacks that brought those sites down. Currently, there is not a count for the number of sites that fell victim to this hack, but multiple cryptocurrency services were on that list, including Liquid.com and NiceHash.
GoDaddy is still investigating how these hackers accomplished this, but it’s likely they relied on “vishing“, voice calls that send their victims to phishing sites to collect sensitive account login information. It’s believed the hackers convinced the GoDaddy staff they were from the victim company’s IT department and were working to resolve technical issues. Unfortunately, the GoDaddy staff believed these hackers and gave them control over the domains. They have since responded by reverting the changes, locking down account access, and helping victims regain access. But this comes nearly a year after a data breach at GoDaddy that affected 28,000 hosting accounts.
This is one of many examples showcasing the sophistication and social engineering modern-day hackers are exercising. Phishing attacks have been on the rise and hackers are taking advantage of employees working from home and a general population of tired and overwhelmed targets. Our goal at QSG is to provide you with the knowledge you need to prevent phishing and vishing attacks to keep your data secure from threats.
What is Vishing?
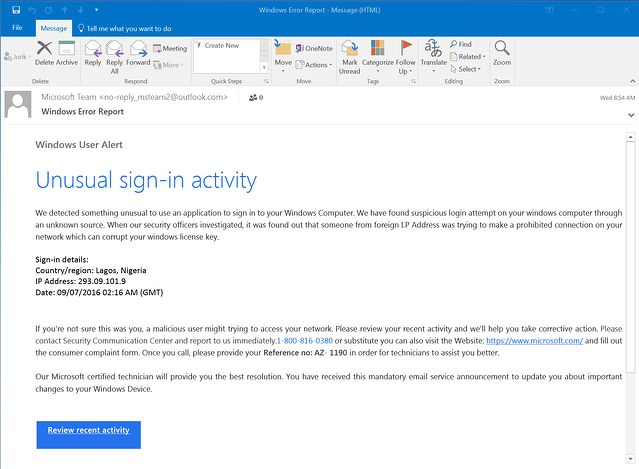
Vishing, or “Voice Phishing”, is the fraudulent practice where scammers make phone calls or leave voice messages pretending to be from reputable companies. Using social engineering, these scammers attempt to get you to share personal information and financial details, such as account numbers, credit cards, and passwords.
It’s very likely you have already experienced a vishing attack – or a spam call – a common one many of us experience is “your car warranty is about to expire” from an automated robot voice call. But we have also heard of calls where scammers say your account has been compromised, claim to be from law enforcement or other federal agencies, and sometimes offer to install software (malware).
Unfortunately, it’s very easy for these scammers to get access to your information and place hundreds of calls at a time, spoofing their caller ID to appear they are calling from a trusted source.
How to Spot a Vishing Attack [1]:
- The caller claims to represent the IRS, Medicare, or the Social Security Administration. Unless you’ve requested contact, none of these federal agencies will ever initiate contact with you by email, text messages, or social media channels to request personal or financial information.
- There’s a frantic sense of urgency. Scammers will try to tap into your sense of fear, using threats of arrest warrants and problems with your account. Rather than give them information, do your own investigation and research.
- The caller asks for your information. They may ask you to confirm your name, address, birth date, Social Security number, bank account info, and other identifying details. To trick you into thinking they’re legit, they may even have some of this info on hand. The goal is to get the remaining info that they don’t have yet.
How to Protect Against a Vishing Attack:
- Join the National Do Not Call Registry. Adding your home or mobile phone number to this registry is free and tells telemarketers you don’t want their phone calls. However, certain types of organizations may still call you, such as charities and political groups, and it won’t stop people from illegally calling your number.
- Don’t pick up the phone. Although it may be tempting to answer every phone call, simply let them go to voicemail. Caller IDs can be spoofed, so instead, listen to your messages and decide whether to call the person back.
- Hang up. The moment you suspect it’s a vishing phone call, don’t feel obliged to carry on a polite conversation. Simply hang up, and block the number.
- Don’t press buttons or respond to prompts. If you get an automated message that asks you to press buttons or respond to questions, don’t do it. Scammers use these tricks to identify potential targets for more robocalls because you were responsive. They may also record your voice and later use it when navigating voice-automated phone menus tied to your accounts.
- Verify the caller’s identity. If the person provides a call-back number, it may be part of the scam — so don’t use it. Instead, search for the company’s official public phone number and call the organization in question.
- Take Advantage of Phone Screens: Not all phones have this feature, but Google Pixel provides the ability to screen any call from a number you do not recognize. It will pick up the call, ask why the person is calling and give you a transcript in real-time so you can choose whether you would like to answer or not. It’s a great service that I personally use, and is extremely helpful to avoid scam callers.
We hope this article provides you with the information you need to stay protected against vishing attacks and phishing attacks. Want to test your knowledge? Try out our phishing quiz here. We also offer phishing campaigns to test your employees and see who would fall for a scam. For more information, please contact us!